Soracom Beam
Configuration
Enabling Beam will incur fees based on the number of requests made. Refer to the Pricing & Fee Schedule for more information.
Soracom Beam settings are found in Soracom Air or Soracom Inventory group settings.
As different Soracom Air and Soracom Inventory devices support different communication protocols, different Beam settings are available depending on the type of device (cellular, Sigfox, LoRaWAN, or Inventory) being configured.
To configure Beam, open the settings page of the group that you want to configure.
From the User Console, click the Menu button, then:
- for Air for Cellular devices, click Groups from the Soracom Air for Cellular section.
- for Air for Sigfox devices, click Sigfox Device Groups from the Soracom Air for Sigfox section.
- for Air for LoRaWAN devices, click LoRa Groups from the Soracom Air for LoRaWAN™ section.
- for Soracom Inventory devices, click Device Groups from the Soracom Inventory section.
Then, from the list of groups in your account, click the group to open its settings page. Underneath the Basic Settings tab, click the SORACOM Beam panel to expand its settings.
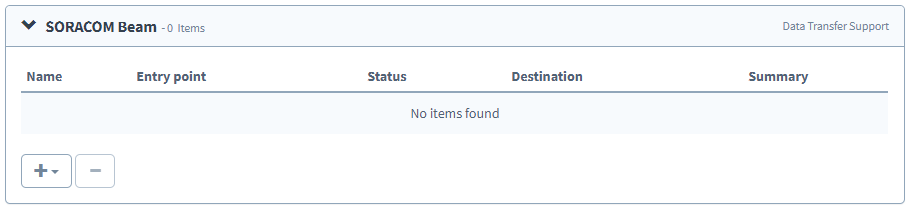
From this panel, click the button to add a Beam configuration. You can also modify and delete configurations for this group from this panel.
Each group can include multiple settings for different device types (Cellular, Sigfox, LoRaWAN, and Inventory). To add Beam configurations for additional device types, simply repeat the above steps for each device type.
Entry Points
Since Soracom Beam supports receiving data from and forwarding data using various protocols, each combination of incoming and outgoing protocols requires different parameters for configuration. These sets of parameters are grouped into rules, which correspond to the desired forwarding behavior.
For each rule, the Entry point is the endpoint where Beam will receive data from your device. You should configure your device to send data to this endpoint. As connections to this endpoint are already secured, no additional encryption or authentication is required from the device.
Each rule will also contain a Destination where Beam will forward data. Depending on protocol, you may need to supply additional credentials in order to authorize connections to the destination.
As the parameters for each Entry point vary according to the destination protocol, configuration details for each entry point are found on their respective documentation pages.
Air for Cellular
| Entry Point | Destination | Address | Description |
|---|---|---|---|
| HTTP | HTTP/HTTPS | http://beam.soracom.io:8888 |
Receive HTTP requests from a device and forward them to your HTTP or HTTPS endpoint |
| Website | HTTP/HTTPS | http://beam.soracom.io:18080 |
Receive HTTP or WebSocket requests from a device and forward them to your HTTP, WS, HTTPS or WSS endpoint. Also it will append any URI from the original request to the forwarded request. |
| MQTT | MQTT/MQTTS | mqtt://beam.soracom.io:1883 |
Receive MQTT actions from a device and forward them to your MQTTS broker using MQTT or MQTTS |
| TCP | TCP/TCPS | tcp://beam.soracom.io:8023 |
Receive TCP packets from a device and forward them to your destination using TCP or TCPS |
| TCP | HTTP/HTTPS | tcp://beam.soracom.io:23080 |
Receive TCP packets from a device, convert them into HTTP or HTTPS requests, and forward the requests to your endpoint |
| UDP | HTTP/HTTPS | udp://beam.soracom.io:23080 |
Receive UDP packets from a device, convert them into HTTP or HTTPS requests, and forward the requests to your endpoint |
| SMS | HTTP/HTTPS | 901011 |
Receive SMS messages from a device, convert them into HTTP or HTTPS requests, and forward the requests to your endpoint |
| USSD | HTTP/HTTPS | *901011*{data}# |
Receive USSD messages from a device, convert them into HTTP or HTTPS requests, and forward the requests to your endpoint |
Air for Sigfox and Air for LoRa
| Entry Point | Destination | Address | Description |
|---|---|---|---|
| Sigfox or LoRa | HTTP/HTTPS | — | Receive data from a Sigfox or LoRa device, convert it into an HTTP or HTTPS request, and forward the request to your endpoint |
Soracom Inventory
| Entry Point | Destination | Address | Description |
|---|---|---|---|
| Inventory | HTTP/HTTPS | — | Receive data from a Soracom Inventory device, convert it into an HTTP or HTTPS request, and forward the request to your endpoint |
Header Manipulation
Depending on device type (cellular, Sigfox, or LoRaWAN) and destination protocol (HTTP/HTTPS, TCP/TCPS, MQTT/MQTTS), you can optionally specify how Beam should modify headers before forwarding connections to your endpoint.
Refer to Header Manipulation for further information.
Signature Verification
In addition to header manipulation, Beam can optionally generate a signature based on subscriber IMSI, device IMEI, timestamp, and a Pre-Shared Key for use with authenticating forwarded data.
Refer to Signature Verification for further information.